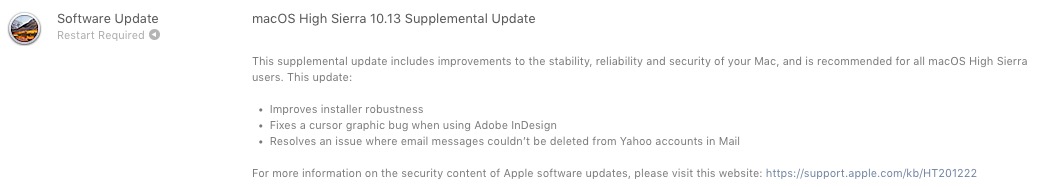
Apple har nyligen publicerat en mycket viktig tilläggsuppdatering för alla Mac-användare som har installerat macOS High Sierra 10.13.
I macOS High Sierra 10.13 tilläggsuppdatering lösa några driftstörningar för Adobe InDesign och en bugg som tillät inte radera meddelanden som tagits emot i Mail-programmet från Yahoo!.
Den allvarligaste delen av uppdateringen ytterligare är relaterad till två säkerhetsproblem, som kom "som ett paket" med det nya operativsystemet High Sierra.
Sårbarhet för krypteringslösenord för APFS (Encrypted) – Disk Utility Bug
En bugg i programmet Skivverktyg Det gör synliga lösenord för volymer på diskar formaterade APFS krypterad.
Kort sagt, när vi anger krypteringslösenordet för en volym efterfrågas det två gånger för att vara säker på att vi inte skrev fel första gången. Då måste vi välja en "Tips” (ett ord eller en fras) som lösenordstips. Buggan in Skivverktyg, gör lösenordet synligt istället för ordet eller frasen från "tips". På så sätt exponeras den för alla som har tillgång till Mac.
I videon som publicerats på Twitter kan du se exakt hur du hittar lösenordet för en APFS-krypterad volym med hjälp av Disk Utility.
Skulle vara intressant varför Apple rekommenderar att radera när diskutil kan rensa tips:
diskutil apfs setPassphraseHint [diskXsX] -användardisk -clear pic.Twitter.com/0khrm8aTq9— Felix Schwarz (@felix_schwarz) 5 oktober 2017
Sårbar nyckelringstillgång – kringgå användarlösenord
Normalt och nödvändigtvis när vi kommer åt ett konto och ett lösenord som sparats i nyckelring, tillfrågas vi användarens lösenord Mac. Genom en sårbarhet a MacOS High Sierra, kan en skadlig applikation Hämta sparade lösenord i Nyckelhanterare, hoppa över Mac-användarlösenordet med hjälp av ett syntetiskt klick. Falsk/simulerad.
Släppt 5 oktober 2017
StorageKit
Tillgänglig för: macOS High Sierra 10.13
Effekt: En lokal angripare kan få tillgång till en krypterad APFS-volym
Beskrivning: Om en ledtråd angavs i Diskverktyget när en APFS-krypterad volym skapades, lagrades lösenordet som ledtråden. Detta åtgärdades genom att rensa tipslagring om ledtråden var lösenordet och genom att förbättra logiken för att lagra tips.
CVE-2017-7149: Matheus Mariano från Leet Tech
Säkerhet
Tillgänglig för: macOS High Sierra 10.13
Effekt: En skadlig applikation kan extrahera nyckelringslösenord
Beskrivning: Det fanns en metod för applikationer att kringgå nyckelringens åtkomstprompt med ett syntetiskt klick. Detta åtgärdades genom att kräva användarlösenordet när man bad om nyckelringstillgång.
CVE-2017-7150: Patrick Wardle från Synack
Nya nedladdningar av macOS High Sierra 10.13 inkluderar säkerhetsinnehållet i macOS High Sierra 10.13 tilläggsuppdatering.
Därför, om du har macOS High Sierra 10.13, rekommenderas det starkt att göra den extra uppdateringen. Den finns tillgänglig via Mac App Store, i tab-ul "Uppdateringar"(och kommer inte att ändra versionsnumret). Apple har redan publicerat macOS High Sierra 10.13.1 för utvecklare som har enheter i Apples betaprogram.






1 tänkte på “Säkerhetsfrågor APF: er krypterade och nyckelringåtkomst, löst med MacOS High Sierra 10.13 Kompletterande uppdatering”