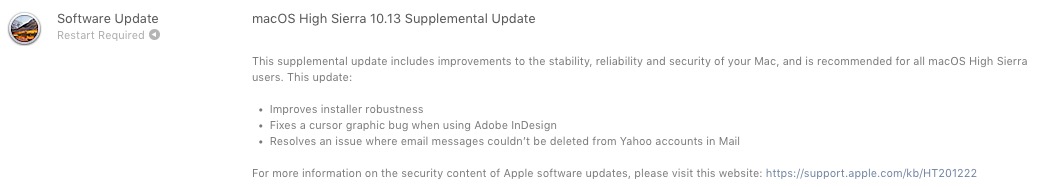
Apple has recently published a very important Supplemental Update for all Mac users who have installed macOS High Sierra 10.13.
In macOS High Sierra 10.13 Supplemental Update are solving some malfunctions for Adobe InDesign and a bug that did not allow deleting messages received in the Mail application from Yahoo!.
The most serious part of this additional update is related to two security issues, which came "as a package" with the new High Sierra operating system.
Encryption password vulnerability for APFS (Encrypted) – Disk Utility Bug
A bug in the application Disk Utility that makes visible password for disk volumes formatted APFS Encrypted.
In short, when we enter the encryption password for a volume, it is requested twice, to be sure that we didn't type it wrong the first time. Then we have to choose a "hint” (a word or phrase) as a password hint. The bug in Disk Utility, makes the password visible instead of the word or phrase from "hint". In this way, it is exposed to anyone who has access to the Mac.
In the video posted on Twitter, you can see exactly how to find the password of an APFS encrypted volume, using Disk Utility.
Would be interesting why Apple recommends erasing when diskutil can clear hints:
diskutil apfs setPassphraseHint [diskXsX] -user disk -clear pic.twitter.com/0khrm8aTq9— Felix Schwarz (@felix_schwarz) October 5, 2017
Vulnerabilitate Keychain Access – bypass user password
Normally and necessarily, when we access an account and a password saved in Keychain, we are asked user password Mac. Through a vulnerability a MacOS High Sierra, a malicious application can retrieve saved passwords in Keychain Access, skipping the Mac user password by means of a synthetic click. Fake / simulated.
Released October 5, 2017
StorageKit
Available for: macOS High Sierra 10.13
Impact: A local attacker may gain access to an encrypted APFS volume
Description: If a hint was set in Disk Utility when creating an APFS encrypted volume, the password was stored as the hint. This was addressed by clearing hint storage if the hint was the password, and by improving the logic for storing hints.
CVE-2017-7149: Matheus Mariano of Leet Tech
Security
Available for: macOS High Sierra 10.13
Impact: A malicious application can extract keychain passwords
Description: A method existed for applications to bypass the keychain access prompt with a synthetic click. This was addressed by requiring the user password when prompting for keychain access.
CVE-2017-7150: Patrick Wardle of Synack
New downloads of macOS High Sierra 10.13 include the security content of the macOS High Sierra 10.13 Supplemental Update.
Therefore, if you have macOS High Sierra 10.13, it is highly recommended to do the additional update. It is available via Mac App Store, in tab-ul “Updates"(and will not change the version number). Apple has already published macOS High Sierra 10.13.1 for developers who have devices in the Apple Beta Software Program.






1 thought on “Security issues APFS ENCRYPTED and Keychain Access, solved with Macos High Sierra 10.13 Supplemental Update"