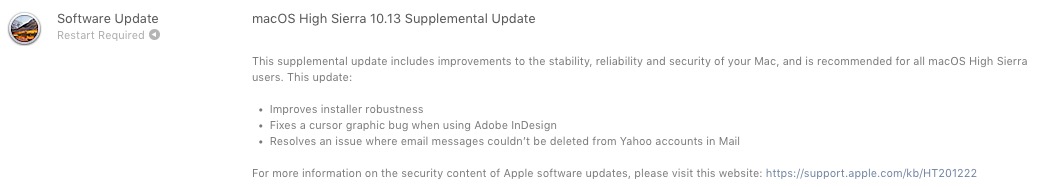
„Apple“ neseniai paskelbė labai svarbų papildomą naujinimą, skirtą visiems įdiegusiems „Mac“ vartotojams macOS High Sierra 10.13.
Į „MacOS High Sierra 10.13“ papildomas atnaujinimas yra sprendžiant kai kuriuos sutrikimus, Adobe InDesign ir a re kurios neleido Pašto programoje gautų pranešimų iš Yahoo!.
Sunkiausias dalis, Šis papildomas naujinimas yra susijęs su du saugumo klausimai, kuris buvo „kaip paketas“ su nauja „High Sierra“ operacine sistema.
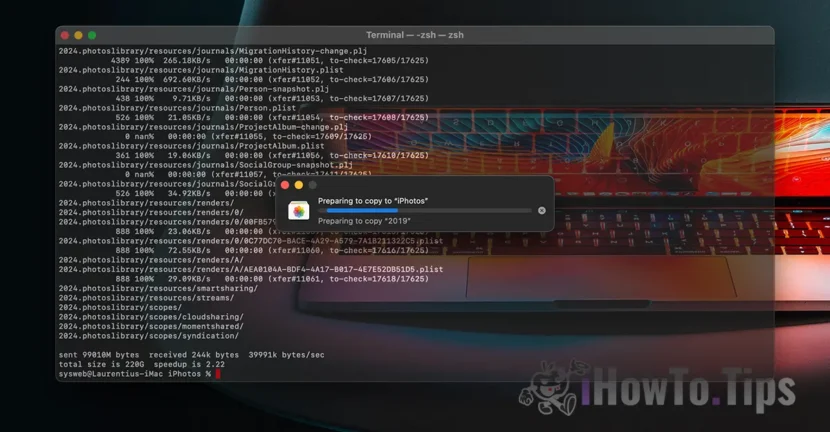
Šifravimo slaptažodžio pažeidžiamumas APFS (šifruotas) – disko paslaugų programos klaida
Klaida, taikant Diskų tai daro matomas slaptažodį Disko tomai formatuojami APFS šifruojama.
Trumpai tariant, kai įvedame tomo šifravimo slaptažodį, jo prašoma du kartus, kad įsitikintume, jog pirmą kartą neįvedėme neteisingai. Tada turime pasirinkti "Patarimas“ (žodis arba frazė) kaip slaptažodžio užuomina. Klaida Diskų, slaptažodis tampa matomas vietoj žodžio ar frazės iš „užuomina“. Tokiu būdu jis yra prieinamas visiems, kurie turi prieigą prie „Mac“.
„Twitter“ paskelbtame vaizdo įraše galite tiksliai pamatyti, kaip naudojant „Disk Utility“ rasti APFS užšifruoto tomo slaptažodį.
Būtų įdomu, kodėl „Apple“ rekomenduoja ištrinti, kai diskutil gali išvalyti užuominas:
diskutil apfs setPassphraseHint [diskXsX] -vartotojo diskas - išvalyti pic.Twitter.com/0khrm8aTq9- Feliksas Schwarzas (@felix_schwarz) 2017 m. Spalio 5 d
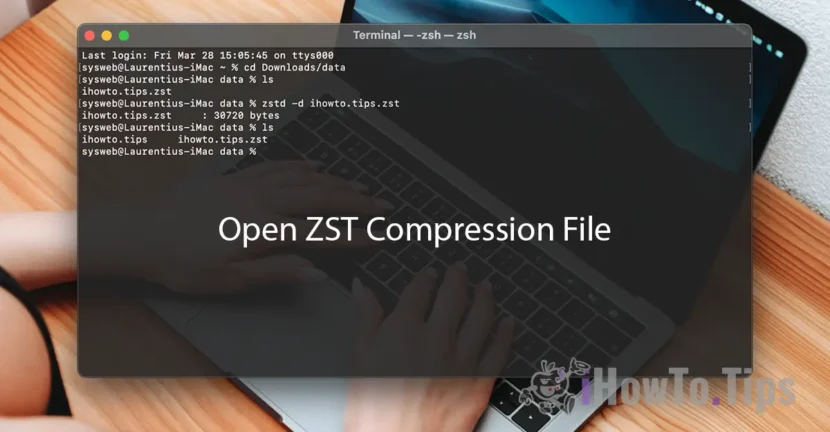
„Vulnerabilitate Keychain Access“ – apeiti vartotojo slaptažodį
Paprastai ir būtinai, kai pasiekiame abonementą ir slaptažodį, išsaugotą raktų pakabukas, mūsų klausia vartotojo slaptažodį "Mac". Dėl pažeidžiamumo a MacOS High Siera, kenkėjiška programa gali nuskaityti įrašytus slaptažodžius Keychain Access, praleisdami „Mac“ vartotojo slaptažodį sintetiniu paspaudimu. Netikras / imituotas.
Išleista 2017 m. spalio 5 d
StorageKit
Galima naudoti: macOS High Sierra 10.13
Poveikis: vietinis užpuolikas gali gauti prieigą prie užšifruoto APFS tomo
Aprašymas: Jei kuriant APFS užšifruotą tomą Disk Utility buvo nustatyta užuomina, slaptažodis buvo išsaugotas kaip užuomina. Tai buvo sprendžiama išvalius užuominų saugyklą, jei užuomina buvo slaptažodis, ir patobulinus užuominų saugojimo logiką.
CVE-2017-7149: Matheusas Mariano iš Leet Tech
Saugumo
Galima naudoti: macOS High Sierra 10.13
Poveikis: kenkėjiška programa gali išgauti raktų pakabuko slaptažodžius
Aprašymas: egzistuoja metodas, skirtas programoms apeiti raktų pakabuko prieigos raginimą sintetiniu paspaudimu. Tai buvo išspręsta reikalaujant vartotojo slaptažodžio, kai raginama prisijungti prie raktų pakabuko.
CVE-2017-7150: Patrick Wardle iš Synack
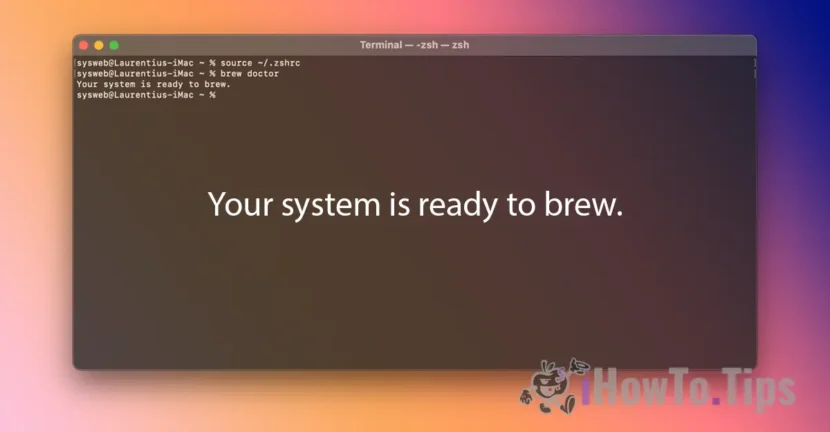
Nauji „macOS High Sierra 10.13“ atsisiuntimai apima „macOS High Sierra 10.13“ papildomo naujinio saugos turinį.
Todėl, jei turite macOS High Sierra 10.13, labai rekomenduojama atlikti papildomą atnaujinimą. Jis pasiekiamas per Mac App Store, tab-ul “Atnaujinimai"(ir nekeis versijos numerio). Apple jau paskelbė macOS High Sierra 10.13.1 kūrėjams, turintiems įrenginius Apple Beta programinės įrangos programoje.






1 galvojo apie “Apsaugos problemos APFS užšifruota ir prieiga"